COMPUTER SCIENCE & APPLICATIONS
PAPER – III
Note : This paper contains seventy five (75) objective type questions of two (2) marks each. All questions are compulsory.
1. Which of the following is an interrupt according to temporal relationship with system clock ?
(1) Maskable interrupt
(2) Periodic interrupt
(3) Division by zero
(4) Synchronous interrupt
2. Which of the following is incorrect for virtual memory ?
(1) Large programs can be written
(2) More I/O is required
(3) More addressable memory available
(4) Faster and easy swapping of process
3. The general configuration of the microprogrammed control unit is given below :
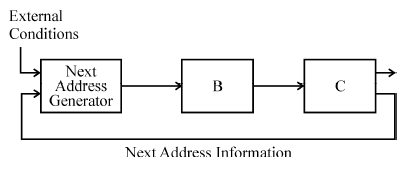
What are blocks B and C in the diagram respectively ?
(1) Block address register and cache memory
(2) Control address register and control memory
(3) Branch register and cache memory
(4) Control address register and random access memory
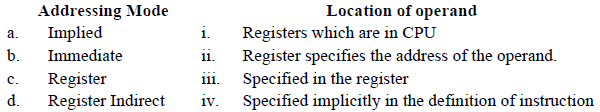
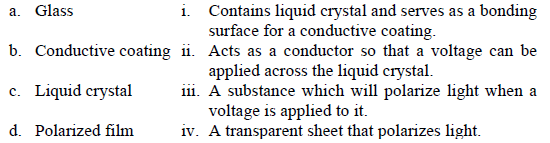
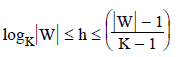
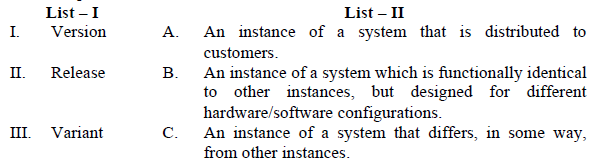
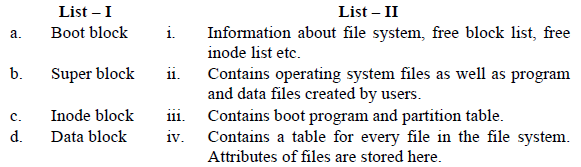
4. Match the following :
5. In 8085 microprocessor, the digit 5 indicates that the microprocessor needs
(1) –5 volts, +5 volts supply
(2) +5 volts supply only
(3) –5 volts supply only
(4) 5 MHz clock
6. In 8085, which of the following performs : load register pair immediate operation ?
(1) LDAX rp
(2) LHLD addr
(3) LXI rp, data
(4) INX rp
7. Consider following schedules involving two transactions :
S1 : r1(X); r1(Y); r2(X); r2(Y); w2(Y); w1(X)
S2 : r1(X); r2(X); r2(Y); w2(Y); r1(Y); w1(X)
Which of the following statement is true ?
(1) Both S1 and S2 are conflict serializable.
(2) S1 is conflict serializable and S2 is not conflict serializable.
(3) S1 is not conflict serializable and S2 is conflict serializable.
(4) Both S1 and S2 are not conflict serializable.
8. Which one is correct w.r.t. RDBMS ?
(1) primary key ⊆ super key ⊆ candidate key
(2) primary key ⊆ candidate key ⊆ super key
(3) super key ⊆ candidate key ⊆ primary key
(4) super key ⊆ primary key ⊆ candidate key
9. Let pk(R) denotes primary key of relation R. A many-to-one relationship that exists between two relations R1 and R2 can be expressed as follows :
(1) pk(R2) → pk(R1)
(2) pk(R1) → pk(R2)
(3) pk(R2) → R1 ∩ R2
(4) pk(R1) → R1 ∩ R2
10. For a database relation R(A, B, C, D) where the domains of A, B, C and D include only atomic values, only the following functional dependencies and those that can be inferred from them are :
A → C
B → D
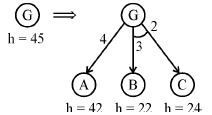
The relation R is in _______.
(1) First normal form but not in second normal form.
(2) Both in first normal form as well as in second normal form.
(3) Second normal form but not in third normal form.
(4) Both in second normal form as well as in third normal form.
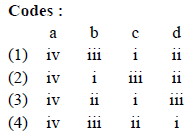
11. Consider the following relation :
The above query is for following :
(1) Find the highest paid employee who earns more than the average salary of all employees of his company.
(2) Find the highest paid employee who earns more than the average salary of all the employees of all the companies.
(3) Find all employees who earn more than the average salary of all employees of all the companies.
(4) Find all employees who earn more than the average salary of all employees of their company.
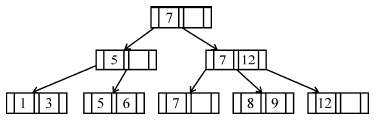
12. If following sequence of keys are inserted in a B+ tree with K(=3) pointers :
8, 5, 1, 7, 3, 12, 9, 6
Which of the following shall be correct B+ tree ?
(1) 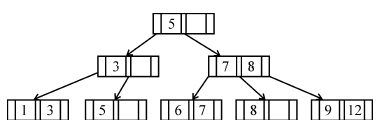
(2) 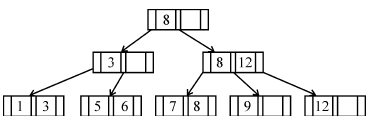
(3) 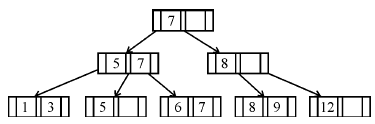
(4) 
13. Which of the following statement(s) is/are correct ?
(1) Persistence is the term used to describe the duration of phosphorescence.
(2) The control electrode is used to turn the electron beam on and off.
(3) The electron gun creates a source of electrons which are focussed into a narrow beam directed at the face of CRT.
(4) All of the above
14. A segment is any object described by GKS commands and data that start with CREATE SEGMENT and Terminates with CLOSE SEGMENT command. What functions can be performed on these segments ?
(1) Translation and Rotation
(2) Panning and Zooming
(3) Scaling and Shearing
(4) Translation, Rotation, Panning and Zooming
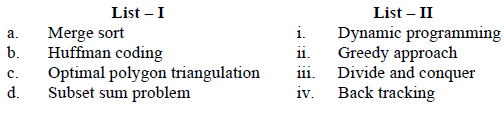
15. Match the following :
16. Below are the few steps given for scan-converting a circle using Bresenham’s Algorithm.
Which of the given steps is not correct ?
(1) Compute d = 3 – 2r (where r is radius)
(2) Stop if x > y
(3) If d < 0, then d = 4x + 6 and x = x + 1
(4) If d ≥ 0, then d = 4 ∗ (x – y) + 10, x = x + 1 and y = y + 1
17. Which of the following is/are side effects of scan conversion ?
a. Aliasing
b. Unequal intensity of diagonal lines
c. Overstriking in photographic applications
d. Local or Global aliasing
(1) a and b
(2) a, b and c
(3) a, c and d
(4) a, b, c and d
18. Consider a line AB with A = (0, 0) and B = (8, 4). Apply a simple DDA algorithm and compute the first four plots on this line.
(1) [(0, 0), (1, 1), (2, 1), (3, 2)]
(2) [(0, 0), (1, 1.5), (2, 2), (3, 3)]
(3) [(0, 0), (1, 1), (2, 2.5), (3, 3)]
(4) [(0, 0), (1, 2), (2, 2), (3, 2)]
19. Which of the following are not regular ?
(A) Strings of even number of a’s.
(B) Strings of a’s, whose length is a prime number.
(C) Set of all palindromes made up of a’s and b’s.
(D) Strings of a’s whose length is a perfect square.
(1) (A) and (B) only
(2) (A), (B) and (C) only
(3) (B), (C) and (D) only
(4) (B) and (D) only
20. Consider the languages L1 = ϕ and L2 = {1}. Which one of the following represents ![]()
(1) {∈}
(2) {∈, 1}
(3) ϕ
(4) 1*
21. Given the following statements :
(A) A class of languages that is closed under union and complementation has to be closed under intersection.
(B) A class of languages that is closed under union and intersection has to be closed under complementation.
Which of the following options is correct ?
(1) Both (A) and (B) are false.
(2) Both (A) and (B) are true.
(3) (A) is true, (B) is false.
(4) (A) is false, (B) is true.
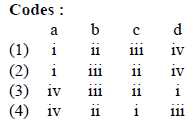
22. Let G = (V, T, S, P) be a context-free grammar such that every one of its productions is of the form A → v, with |v| = K > 1. The derivation tree for any W ∈ L(G) has a height h such that
(1) 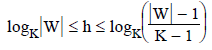
(2) logK|W| ≤ h ≤ logK(K|W|)
(3) logK|W| ≤ h ≤ K logK|W|
(4) 
23. Given the following two languages :
L1 = {an bn | n ≥ 0, n ≠ 100}
L2 = {w ∈ {a, b, c}*| na(w) = nb(w) = nc(w)}
Which of the following options is correct ?
(1) Both L1 and L2 are not context free language
(2) Both L1 and L2 are context free language.
(3) L1 is context free language, L2 is not context free language.
(4) L1 is not context free language, L2 is context free language.
24. A recursive function h, is defined as follows :
h(m) = k, if m = 0
= 1, if m = 1
= 2 h(m – 1) + 4h(m – 2), if m ≥ 2
If the value of h(4) is 88 then the value of k is :
(1) 0
(2) 1
(3) 2
(4) –1
25. Suppose there are n stations in a slotted LAN. Each station attempts to transmit with a probability P in each time slot. The probability that only one station transmits in a given slot is _______.
(1) nP(1 – P)n – 1
(2) nP
(3) P(1 – P)n – 1
(4) nP(1 – P)n – 1
26. Station A uses 32 byte packets to transmit messages to station B using sliding window protocol. The round trip delay between A and B is 40 milliseconds and the bottleneck bandwidth on the path between A and B is 64 kbps. The optimal window size of A is ________.
(1) 20
(2) 10
(3) 30
(4) 40
27. Let G(x) be generator polynomial used for CRC checking. The condition that should be satisfied by G(x) to correct odd numbered error bits, will be :
(1) (1 + x) is factor of G(x)
(2) (1 – x) is factor of G(x)
(3) (1 + x2) is factor of G(x)
(4) x is factor of G(x)
28. In a packet switching network, if the message size is 48 bytes and each packet contains a header of 3 bytes. If 24 packets are required to transmit the message, the packet size is ________.
(1) 2 bytes
(2) 1 byte
(3) 4 bytes
(4) 5 bytes
29. In RSA public key cryptosystem suppose n = p ∗ q where p and q are primes. (e, n) and (d, n) are public and private keys respectively. Let M be an integer such that o < M < n and ϕ(n) = (p – 1) (q – 1).
Which of the following equations represent RSA public key cryptosystem ?
I. C ≡ Me (mod n)
M ≡ (C)d (mod n)
II. ed ≡ 1(mod n)
III. ed ≡ 1(mod ϕ(n))
IV. C ≡ Me(mod ϕ(n))
M ≡ Cd(mod ϕ(n))
Codes :
(1) I and II
(2) I and III
(3) II and III
(4) I and IV
30. A node X on a 10 Mbps network is regulated by a token bucket. The token bucket is filled at a rate of 2 Mbps. Token bucket is initially filled with 16 megabits. The maximum duration taken by X to transmit at full rate of 10 Mbps is _________ secs.
(1) 1
(2) 2
(3) 3
(4) 4
31. The asymptotic upper bound solution of the recurrence relation given by ![]() is :
is :
(1) O(n2)
(2) O(n lg n)
(3) O(n lg lg n)
(4) O(lg lg n)
32. Any decision tree that sorts n elements has height ________.
(1) Ω(lg n)
(2) Ω(n)
(3) Ω(n lg n)
(4) Ω(n2)
33. Red-black trees are one of many search tree schemes that are “balanced” in order to guarantee that basic dynamic-set operations take ________ time in the worst case.
(1) O(1)
(2) O(lg n)
(3) O(n)
(4) O(n lg n)
34. The minimum number of scalar multiplication required, for parenthesization of a matrixchain product whose sequence of dimensions for four matrices is <5, 10, 3, 12, 5> is
(1) 630
(2) 580
(3) 480
(4) 405
35. Dijkstra’s algorithm is based on
(1) Divide and conquer paradigm
(2) Dynamic programming
(3) Greedy Approach
(4) Backtracking paradigm
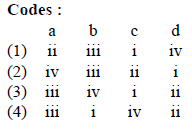
36. Match the following with respect to algorithm paradigms :
37. Abstraction and encapsulation are fundamental principles that underlie the object oriented approach to software development. What can you say about the following two statements ?
I. Abstraction allows us to focus on what something does without considering the complexities of how it works.
II. Encapsulation allows us to consider complex ideas while ignoring irrelevant detail that would confuse us.
(1) Neither I nor II is correct.
(2) Both I and II are correct.
(3) Only II is correct.
(4) Only I is correct.
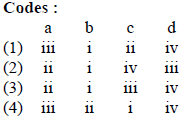
38. Given the array of integers ‘array’ shown below :
(1) 20 : 20
(2) 18 : 18
(3) 18 : 20
(4) 20 : 18
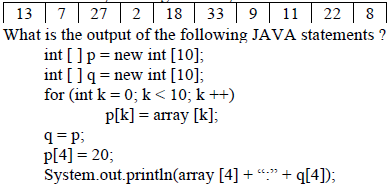
39. Consider the following JAVA program :
What does this program print ?
(1) 59
(2) 95
(3) 69
(4) 99
40. Which of the following statement(s) with regard to an abstract class in JAVA is/are TRUE ?
I. An abstract class is one that is not used to create objects.
II. An abstract class is designed only to act as a base class to be inherited by other classes.
(1) Only I
(2) Only II
(3) Neither I nor II
(4) Both I and II
41. Which of the following HTML code will affect the vertical alignment of the table content ?
(1) <td style = “vertical-align : middle”> Text Here </td>
(2) <td valign = “centre”> Text Here </td>
(3) <td style = “text-align : center”> Text Here </td>
(4) <td align = “middle”> Text Here </td>
42. What can you say about the following statements ?
I. XML tags are case-insensitive.
II. In JavaScript, identifier names are case-sensitive.
III. Cascading Style Sheets (CSS) cannot be used with XML.
IV. All well-formed XML documents must contain a document type definition.
(1) only I and II are false.
(2) only III and IV are false.
(3) only I and III are false.
(4) only II and IV are false.
43. Which of the following statement(s) is/are TRUE with regard to software testing ?
I. Regression testing technique ensures that the software product runs correctly after the changes during maintenance.
II. Equivalence partitioning is a white-box testing technique that divides the input domain of a program into classes of data from which test cases can be derived.
(1) only I
(2) only II
(3) both I and II
(4) neither I nor II
44. Which of the following are facts about a top-down software testing approach ?
I. Top-down testing typically requires the tester to build method stubs.
II. Top-down testing typically requires the tester to build test drivers.
(1) only I
(2) Only II
(3) Both I and II
(4) Neither I nor II
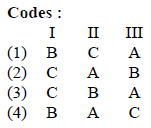
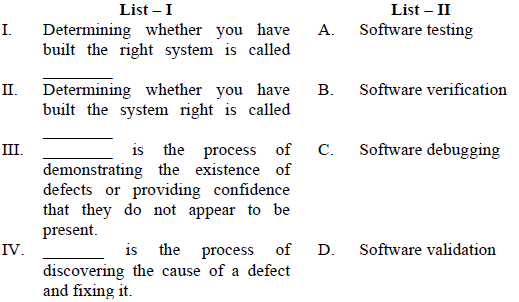
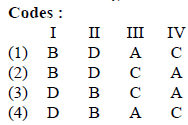
45. Match the terms related to Software Configuration Management (SCM) in List – I with the descriptions in List – II.
46. A software project was estimated at 352 Function Points (FP). A four person team will be assigned to this project consisting of an architect, two programmers, and a tester. The salary of the architect is Rs. 80,000 per month, the programmer Rs. 60,000 per month and the tester Rs. 50,000 per month. The average productivity for the team is 8 FP per personmonth. Which of the following represents the projected cost of the project ?
(1) Rs. 28,16,000
(2) Rs. 20,90,000
(3) Rs. 26,95,000
(4) Rs. 27,50,000
47. Complete each of the following sentences in List – I on the left hand side by filling in the word or phrase from the List – II on the right hand side that best completes the sentence :
48. A software company needs to develop a project that is estimated as 1000 function points and is planning to use JAVA as the programming language whose approximate lines of code per function point is accepted as 50. Considering a = 1.4 as multiplicative factor, b = 1.0 as exponention factor for the basic COCOMO effort equation and c = 3.0 as multiplicative factor, d = 0.33 as exponention factor for the basic COCOMO duration equation, approximately how long does the project take to complete ?
(1) 11.2 months
(2) 12.2 months
(3) 13.2 months
(4) 10.2 months
49. A memory management system has 64 pages with 512 bytes page size. Physical memory consists of 32 page frames. Number of bits required in logical and physical address are respectively :
(1) 14 and 15
(2) 14 and 29
(3) 15 and 14
(4) 16 and 32
50. Consider a disk queue with I/O requests on the following cylinders in their arriving order :
6, 10, 12, 54, 97, 73, 128, 15, 44, 110, 34, 45
The disk head is assumed to be at cylinder 23 and moving in the direction of decreasing number of cylinders. Total number of cylinders in the disk is 150. The disk head movement using SCAN-scheduling algorithm is :
(1) 172
(2) 173
(3) 227
(4) 228
51. Match the following for Unix file system :
52. Some of the criteria for calculation of priority of a process are :
a. Processor utilization by an individual process.
b. Weight assigned to a user or group of users.
c. Processor utilization by a user or group of processes
In fair share scheduler, priority is calculated based on :
(1) only (a) and (b)
(2) only (a) and (c)
(3) (a), (b) and (c)
(4) only (b) and (c)
53. One of the disadvantages of user level threads compared to Kernel level threads is
(1) If a user level thread of a process executes a system call, all threads in that process are blocked.
(2) Scheduling is application dependent.
(3) Thread switching doesn’t require kernel mode privileges.
(4) The library procedures invoked for thread management in user level threads are local procedures.
54. Which statement is not correct about “init” process in Unix ?
(1) It is generally the parent of the login shell.
(2) It has PID 1.
(3) It is the first process in the system
(4) Init forks and execs a ‘getty’ process at every port connected to a terminal.
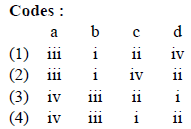
55. Consider following two rules R1 and R2 in logical reasoning in Artificial Intelligence (AI) :
(1) Only R1 is correct.
(2) Only R2 is correct.
(3) Both R1 and R2 are correct.
(4) Neither R1 nor R2 is correct.
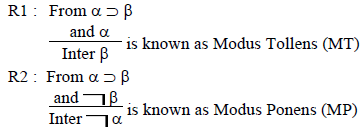
56. Consider the following AO graph :
Which is the best node to expand next by AO* algorithm ?
(1) A
(2) B
(3) C
(4) B and C
57. In Artificial Intelligence (AI), what is present in the planning graph ?
(1) Sequence of levels
(2) Literals
(3) Variables
(4) Heuristic estimates
58. What is the best method to go for the game playing problem ?
(1) Optimal Search
(2) Random Search
(3) Heuristic Search
(4) Stratified Search
59. Which of the following statements is true ?
(1) The sentence S is a logical consequence of S1,…, Sn if and only if S1 ∧ S2 ∧…….. ∧ Sn → S is satisfiable.
(2) The sentence S is a logical consequence of S1,…, Sn if and only if S1 ∧ S2 ∧…….. ∧ Sn → S is valid.
(3) The sentence S is a logical consequence of S1,…, Sn if and only if S1 ∧ S2 ∧…….. ∧ Sn ∧ ¬ S is consistent.
(4) The sentence S is a logical consequence of S1,…, Sn if and only if S1 ∧ S2 ∧…….. ∧ Sn ∧ S is inconsistent.
60. The first order logic (FOL) statement ((R ∨ Q) ∧ (P ∨ ¬ Q)) is equivalent to which of the following ?
(1) ((R ∨ ¬ Q) ∧ (P ∨ ¬ Q) ∧ (R ∨ P))
(2) ((R ∨ Q) ∧ (P ∨ ¬ Q) ∧ (R ∨ P))
(3) ((R ∨ Q) ∧ (P ∨ ¬ Q) ∧ (R ∨ ¬ P))
(4) ((R ∨ Q) ∧ (P ∨ ¬ Q) ∧ ( R ∨ ¬ P))
61. Given the following two statements :
A. L = {w|na(w) = nb(w)} is deterministic context free language, but not linear.
B. L = {an bn} ∪ {an b2n} is linear, but not deterministic context free language.
Which of the following options is correct ?
(1) Both (A) and (B) are false.
(2) Both (A) and (B) are true.
(3) (A) is true, (B) is false.
(4) (A) is false, (B) is true.
62. Which of the following pairs have different expressive power ?
(1) Single-tape-turing machine and multi-dimensional turing machine.
(2) Multi-tape turing machine and multi-dimensional turing machine.
(3) Deterministic push down automata and non-deterministic pushdown automata.
(4) Deterministic finite automata and Non-deterministic finite automata
63. Which of the following statements is false ?
(1) Every context-sensitive language is recursive.
(2) The set of all languages that are not recursively enumerable is countable.
(3) The family of recursively enumerable languages is closed under union.
(4) The families of recursively enumerable and recursive languages are closed under reversal.
64. Let C be a binary linear code with minimum distance 2t + 1 then it can correct upto _____ bits of error.
(1) t + 1
(2) t
(3) t – 2
(4) t/2
65. A t-error correcting q-nary linear code must satisfy :
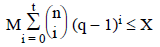
Where M is the number of code words and X is
(1) qn
(2) qt
(3) q–n
(4) q–t
66. Names of some of the Operating Systems are given below :
(a) MS-DOS
(b) XENIX
(c) OS/2
In the above list, following operating systems didn’t provide multiuser facility.
(1) (a) only
(2) (a) and (b) only
(3) (b) and (c) only
(4) (a), (b) and (c)
67. From the given data below :
a b b a a b b a a b
which one of the following is not a word in the dictionary created by LZ-coding (the initial words are a, b) ?
(1) a b
(2) b b
(3) b a
(4) b a a b
68. With respect to a loop in the transportation table, which one of the following is not correct ?
(1) Every loop has an odd no. of cells and atleast 5.
(2) Closed loops may or may not be square in shape.
(3) All the cells in the loop that have a plus or minus sign, except the starting cell, must be occupied cells.
(4) Every loop has an even no. of cells and atleast four.
69. At which of the following stage(s), the degeneracy do not occur in transportation problem ?
(m, n represents number of sources and destinations respectively)
(a) While the values of dual variables ui and vj cannot be computed.
(b) While obtaining an initial solution, we may have less than m + n – 1 allocations.
(c) At any stage while moving towards optimal solution, when two or more occupied cells with the same minimum allocation become unoccupied simultaneously.
(d) At a stage when the no. of +ve allocation is exactly m + n – 1.
(1) (a), (b) and (c)
(2) (a), (c) and (d)
(3) (a) and (d)
(4) (a), (b), (c) and (d)
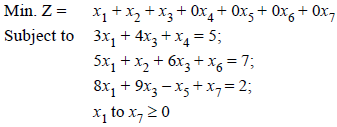
70. Consider the following LPP :
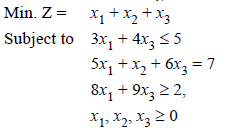
The standard form of this LPP shall be :
(1) 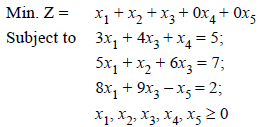
(2) 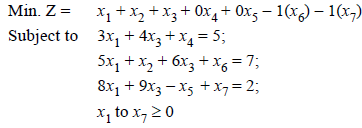
(3) 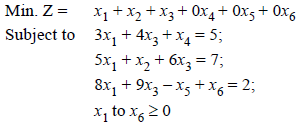
(4) 
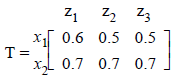
71. Let R and S be two fuzzy relations defined as :
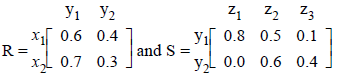
Then, the resulting relation, T, which relates elements of universe x to the elements of universe z using max-min composition is given by :
(1) 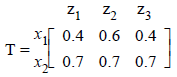
(2) 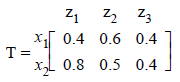
(3) 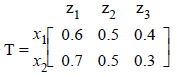
(4) 
72. A neuron with 3 inputs has the weight vector [0.2 –0.1 0.1]T and a bias θ = 0. If the input vector is X = [0.2 0.4 0.2]T then the total input to the neuron is :
(1) 0.20
(2) 1.0
(3) 0.02
(4) –1.0
73. Which of the following neural networks uses supervised learning ?
(A) Multilayer perceptron
(B) Self organizing feature map
(C) Hopfield network
(1) (A) only
(2) (B) only
(3) (A) and (B) only
(4) (A) and (C) only
74. Unix command to change the case of first three lines of file “shortlist” from lower to upper
(1) $ tr ‘[a – z]’ ‘[A – Z]’ shortlist ¦ head-3
(2) $ head-3 shortlist ¦ tr ‘[a – z]’ ‘[A – Z]’
(3) $ tr head -3 shortlist ‘[A – Z]’ ‘[a – z]’
(4) $ tr shortlist head -3 ‘[a – z]’ ‘[A – Z]’
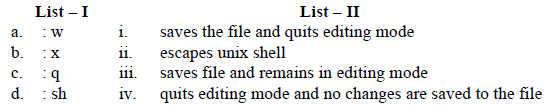
75. Match the following vi commands in Unix :
Latest Govt Job & Exam Updates: